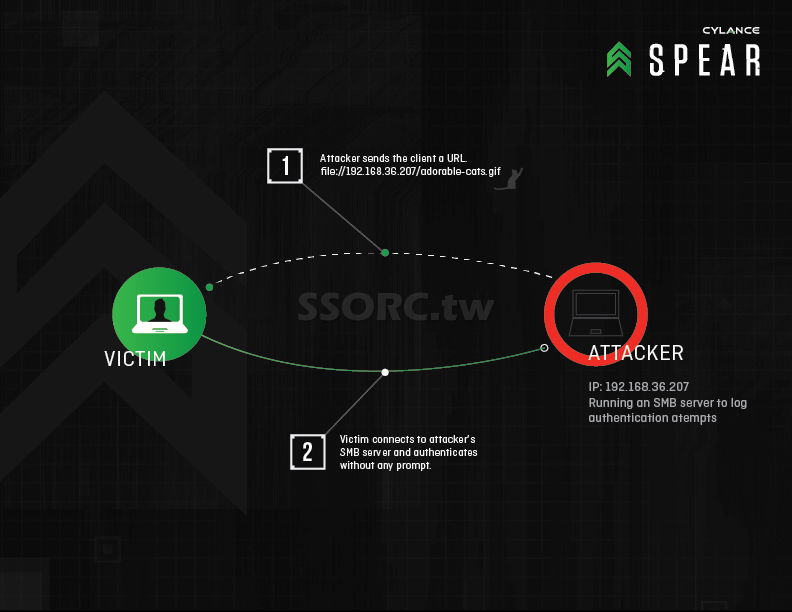
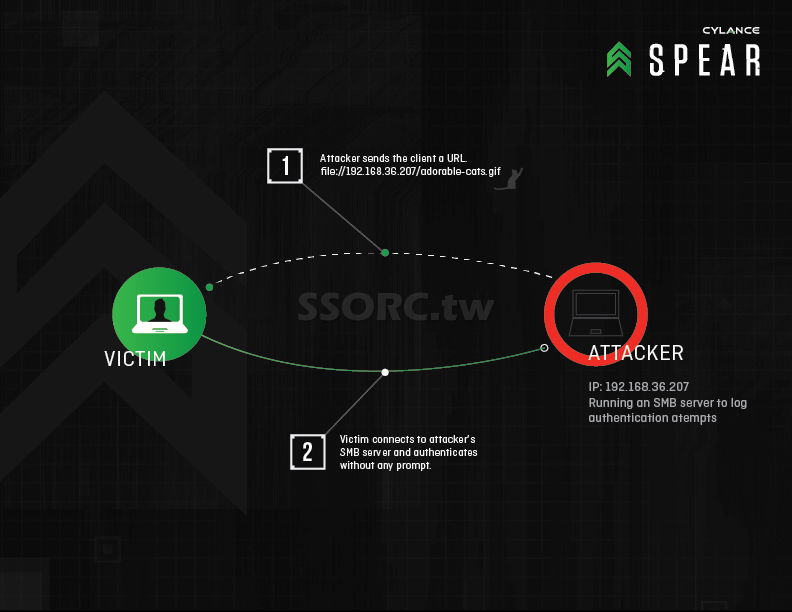
(圖片來自 SPEAR – Redirect to SMB)
怎麼攻擊
就是你點了 file://xxxxxxx 連結, 然後被了中間人攻擊,認證動作被導到不明的 server,windows 就自動的認同這台 server。這個能被偷到帳號密碼。
誰被影響
- Many widely used applications: Adobe Reader, Apple QuickTime and Apple Software Update that handles iTunes updates
- Microsoft Applications: Internet Explorer, Windows Media Player, Excel 2010, and even Microsoft Baseline Security Analyzer
- Developer Tools: Github for Windows, PyCharm, IntelliJ IDEA, PHP Storm and JDK 8u31’s installer
- Security Tools: .NET Reflector and Maltego CE
Antivirus Software: Symantec’s Norton Security Scan, AVG Free, BitDefender Free and Comodo Antivirus - Team Tools: Box Sync and TeamViewer
怎麼防護
- 關閉內到外的 TCP 139 port 及 TCP 445 port
- 更新軟體
- 使用強一點的密碼
參考 18-year-old Unpatched Vulnerability Affects All Versions of Microsoft Windows
留言